With the effective use of the solution applications we recommend, the efficiency of your organization will increase and the necessary environment will be created for you to make the right decisions quickly in an increasingly competitive environment.
- Who are we ?
-
Our Solutions
IT Infrastructure and Operations Services with Modern Solutions
- Desktop Support Services
- Server Support Services
- Empower Your Business with Data Center Management and Storage Services
- Data Center Design and Installation
- Data Center Migration Services
- Structured Cabling Services
- Physical Security Services
- Secure Room Design & Installation
- Maintenance & Repair Services
- MDM Solutions
Information Security Management Services
- Information Security Consulting
- Establishment of ISO 27001 Standard Infrastructure
- Personal Data Protection Services
- Penetration Testing Services
- Event Monitoring and Management Systems
- Logging and SIEM Solutions
- End-User Security
- Hotspot Solution
- Database Security
- Microsoft Security Assessments
- Network Security
IT Audit and KVKK Consultancy
- Compliance Consultancy for Law No. 6698 (KVKK – Turkish Personal Data Protection Law)
- Compliance Consultancy for Law No. 5651
- Pre-Audit Consultancy for ISO 22301
- ISO 27001 Pre-Audit Consultancy
- Pre-Audit Consultancy for SKS
- Capital Markets Board (CMB) Pre-Audit Advisory Services
- Information Technology Audit Consulting
- KVKK, Compliance, and Process Consulting
Artificial Intelligence (AI) Systems
- Enterprise Software & Platform Development
- IT Infrastructure, DevOps, and Security
- Blockchain-Based Systems
- Training, Support, and Transformation Consulting
- Customer Experience (CX) and User Interface (UI/UX) Design
- Data Management, Advanced Analytics, and Business Intelligence Strategies
- Internet of Things (IoT) Solutions
- Cloud-Native Architecture and Development
- API Management and Integration Services
- Fintech & Payment Systems Integrations
- Digital Transformation-Oriented Innovation and R\&D Consulting
-
Our Solutions
- IT Consultancy Services
- IT Security Services
- Software and Support Services
- Data Protection Law Consultancy
-
IT Infrastructure and Operations Services with Modern Solutions
- Desktop Support Services
- Server Support Services
- Empower Your Business with Data Center Management and Storage Services
- Data Center Design and Installation
- Data Center Migration Services
- Structured Cabling Services
- Physical Security Services
- Secure Room Design & Installation
- Maintenance & Repair Services
- MDM Solutions
-
Information Security Management Services
- Information Security Consulting
- Establishment of ISO 27001 Standard Infrastructure
- Personal Data Protection Services
- Penetration Testing Services
- Event Monitoring and Management Systems
- Logging and SIEM Solutions
- End-User Security
- Hotspot Solution
- Database Security
- Microsoft Security Assessments
- Network Security
-
IT Audit and KVKK Consultancy
- Compliance Consultancy for Law No. 6698 (KVKK – Turkish Personal Data Protection Law)
- Compliance Consultancy for Law No. 5651
- Pre-Audit Consultancy for ISO 22301
- ISO 27001 Pre-Audit Consultancy
- Pre-Audit Consultancy for SKS
- Capital Markets Board (CMB) Pre-Audit Advisory Services
- Information Technology Audit Consulting
- KVKK, Compliance, and Process Consulting
- Digital Transformation and Consulting Services
- Data Centre Server Hosting Services
- Business Continuity and Risk Management Consulting
-
Artificial Intelligence (AI) Systems
- Enterprise Software & Platform Development
- IT Infrastructure, DevOps, and Security
- Blockchain-Based Systems
- Training, Support, and Transformation Consulting
- Customer Experience (CX) and User Interface (UI/UX) Design
- Data Management, Advanced Analytics, and Business Intelligence Strategies
- Internet of Things (IoT) Solutions
- Cloud-Native Architecture and Development
- API Management and Integration Services
- Fintech & Payment Systems Integrations
- Digital Transformation-Oriented Innovation and R\&D Consulting
- Blog
- Communication
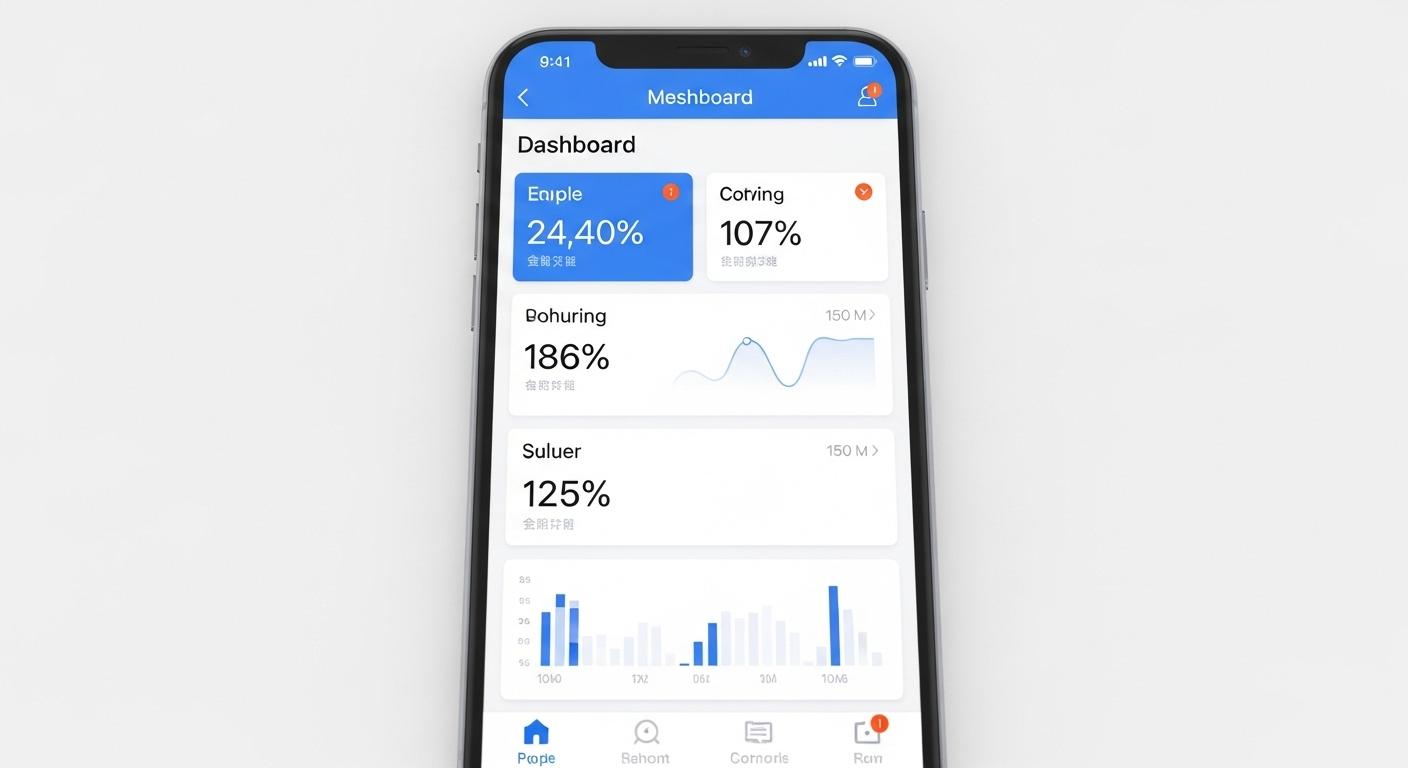
MDM Solutions
MDM Solutions
How Do We Work?
Mobil Cihazları Güvende Tutun - MDM Hizmetleri İle Tanışın
Günümüzde iş dünyası giderek mobil hale gelirken, mobil cihazların etkili bir şekilde yönetimi ve güvenliği işletmeler için kritik bir öneme sahiptir. Firmamız, Müşteri Cihazı Yönetimi (MDM) hizmetleri ile müşterilerine, mobil cihazlarını güvenli bir şekilde yönetmeleri ve iş süreçlerini optimize etmeleri için çözümler sunmaktadır.
Hizmetlerimiz:
Cihaz Yönetimi ve Takip: Mobil cihazları uzaktan yöneterek, güvenlik politikalarını uyguluyor ve cihazlar üzerinde tam kontrole sahip olmanızı sağlıyoruz. Konum takibi, cihaz kilitleme ve silme gibi özelliklerle cihazlarınızı güvence altına alıyoruz.
Uygulama Yönetimi: İşletmeniz için uygun olan uygulamaları belirleyip dağıtıyor, güncelliyor ve gerektiğinde kaldırıyoruz. Uygulama yönetimi ile lisanslama, uyumluluk ve güvenlik konularında kontrol sağlıyoruz.
Veri Güvenliği ve Şifreleme: Hassas verilerinizi güvence altına almak adına cihazlar üzerinde şifreleme ve veri koruma önlemleri uyguluyoruz. Veri sızıntısı riskini en aza indirerek işletmenizin güvenliğini sağlıyoruz.
Güvenlik Politikaları ve Uyum: İşletmenizin ihtiyaçlarına uygun güvenlik politikalarını belirliyor ve uyguluyoruz. Aynı zamanda sektörel uyumluluk standartlarına da dikkat ederek, işletmenizin yasal gereksinimlere uyumlu olmasını sağlıyoruz.
7/24 Destek ve İzleme: Cihazlarınızla ilgili olası sorunlara anında müdahale ediyor ve 7/24 izleme ile güvenlik tehditlerini sürekli olarak değerlendiriyoruz.
Keep Mobile Devices Secure – Discover Our MDM Services
As the business world becomes increasingly mobile, effective management and security of mobile devices have become critically important. Our company offers Mobile Device Management (MDM) services to help clients securely manage their mobile devices and optimize their business processes.
Our Services:
-
Device Management and Tracking
We remotely manage mobile devices, enforce security policies, and give you full control over your fleet. Features like location tracking, remote locking, and wiping help secure your devices. -
Application Management
We identify, deploy, update, and remove applications tailored to your business needs. This ensures control over licensing, compliance, and security. -
Data Security and Encryption
We implement encryption and data protection measures on devices to safeguard sensitive information, minimizing the risk of data leaks and securing your business. -
Security Policies and Compliance
We define and apply security policies based on your organization’s needs while ensuring alignment with industry compliance standards and legal requirements. -
24/7 Support and Monitoring
We provide real-time intervention for potential issues and continuously monitor devices around the clock to evaluate and respond to security threats.


 MDM Solutions
MDM Solutions